The five most common risks of poor user account provisioning and how modern IAM practices reduce security gaps, compliance failures, operational costs, and access management complexity.
The five most common risks of poor user account provisioning and how modern IAM practices reduce security gaps, compliance failures, operational costs, and access management complexity.
User account provisioning refers to the processes used to manage user accounts, credentials, roles, and access rights in IT environments.
User account provisioning occurs in two phases:
Provisioning: Tools and processes for creating and maintaining user accounts, assigning roles, and granting access to organizational data, applications, and cloud services.
De-provisioning: Tools and processes for removing user accounts and revoking access to enterprise systems.
User account provisioning is a multi-step process performed across multiple platforms using either vendor-specific account management tools or cross-platform Identity and Access Management (IAM) solutions.
Poor user account provisioning introduces significant risk, including data security threats, compliance violations, legal exposure, financial losses, and operational inefficiencies.
To create a more secure and effective Identity and Access Management environment, below are five common user account provisioning risks, followed by strategies to mitigate or avoid them.
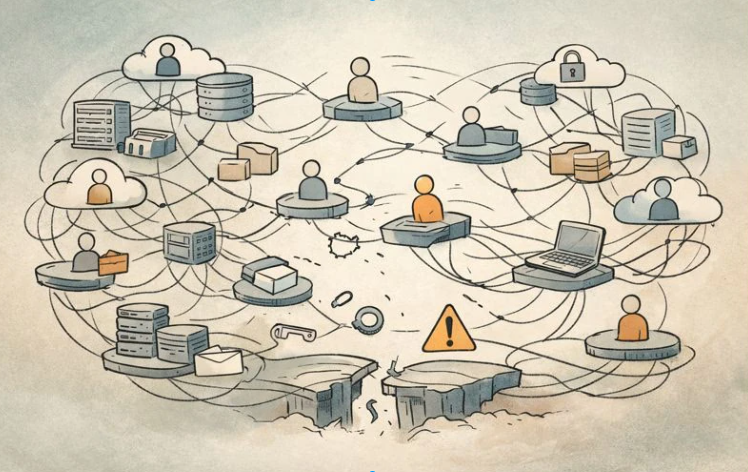
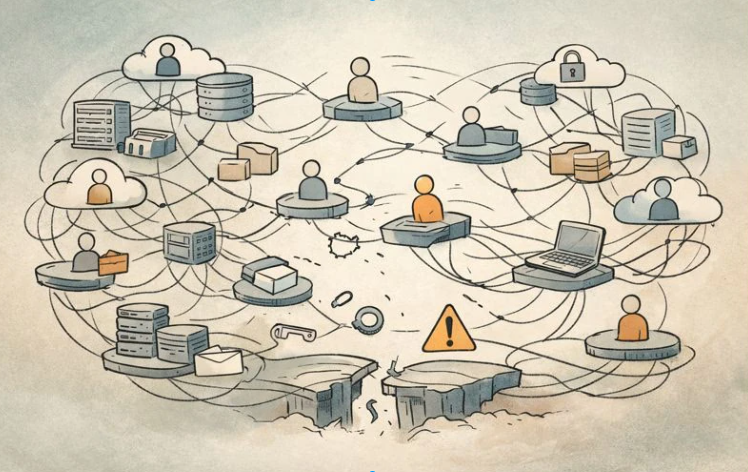
Without a centralized IAM system, user account provisioning often becomes fragmented across multiple tools and platforms.
Organizations may need to create user accounts in Microsoft environments, Amazon Web Services, Google Cloud, Linux systems, legacy platforms, and other servers. Additional accounts may also exist in SaaS applications such as ADP, Salesforce, email systems, and other cloud services.
Managing the same user across multiple provisioning tools increases the likelihood of configuration errors, inconsistent access permissions, over- or under-provisioning, and security gaps.
Industry estimates suggest that the average employee maintains 4–8 user accounts, while highly connected users may have many more.
As account volume increases, IT service desk workloads grow. Typical IT staff-to-user ratios range from 1:50 to 1:200, depending on organization size and regulatory requirements. High provisioning demand drives higher staffing costs, onboarding delays, provisioning backlogs, and reduced employee productivity.
Manual provisioning introduces a high risk of errors and misconfigurations across servers, applications, and cloud services.
Improper access permissions can expose sensitive data to unauthorized users or malicious actors, increasing the likelihood of cyberattacks, ransomware incidents, and data breaches.
Security issues are more difficult to detect when access is granted individually across multiple systems. Role-based approaches—such as RBAC, DAC, or MAC—allow administrators to manage access more efficiently by adjusting role memberships, access control lists, or policies.
Failure to promptly de-provision accounts can result in orphaned or ghost accounts, which may remain accessible after employees leave the organization.
Over-provisioning occurs when users receive more access than required, either due to provisioning mistakes or uncontrolled delegation of authority—particularly in cloud and SaaS environments.
Access drift happens when over-provisioned users grant excessive permissions to others without proper review or approval. This unapproved expansion of access can be difficult to detect and may not appear in standard audit reports.
Many vendor-specific provisioning tools lack comprehensive auditing and reporting capabilities, resulting in limited visibility into account changes.
Low visibility reduces accountability and makes it difficult to demonstrate compliance with governmental, regulatory, and industry requirements. Fragmented provisioning environments further complicate audit reporting and increase compliance risk.
Organizations can reduce or eliminate these risks by adopting the following strategies:
Deploy centralized IAM solutions (such as Tello IAM) that use APIs to manage user accounts across servers, applications, and cloud platforms.
Use IAM platforms with built-in auditing and reporting to improve visibility and compliance.
Leverage automation, workflows, scripting, and artificial intelligence to standardize provisioning and reduce manual errors.
Implement single sign-on (SSO) to reduce the number of accounts that must be provisioned and managed.
Adopt role-based and policy-driven access models (RBAC, DAC, MAC) to assign permissions through roles and policies rather than individual user grants.