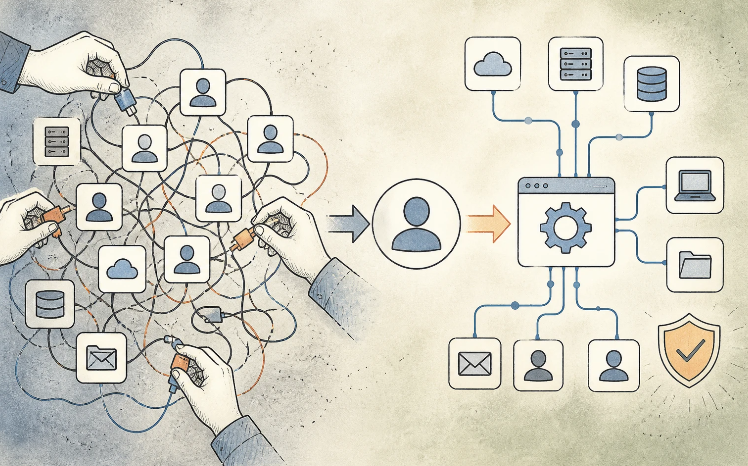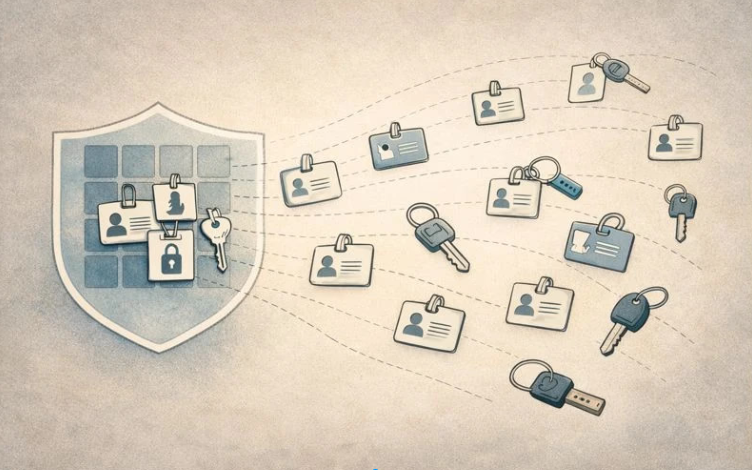
How IAM User Provisioning Enables Identity Governance and Compliance
Learn how IAM user provisioning supports identity governance and compliance by automating lifecycle management, enforcing least-privilege access, and providing monitoring, auditing, and access oversight.