How IAM User Provisioning Enables Identity Governance and Compliance
Learn how IAM user provisioning supports identity governance and compliance by automating lifecycle management, enforcing least-privilege access, and providing monitoring, auditing, and access oversight.
How Identity Governance & Administration and Access Governance Compliance Fit into IAM User Provisioning
This article defines what Identity Governance and Administration (IGA) and Access Governance and Compliance (AGC) are, what roles they play in organizational security, and how Identity and Access Management (IAM) user provisioning solutions fit into an organization’s IGA and AGC requirements.
What is IGA and AGC?
Identity Governance and Administration (IGA) is a comprehensive security framework for IT user identity management. IGA features are a core component for Identity and Access Management (IAM) solutions such as Tello. IGA focuses on managing user accounts and their access permissions throughout the user identity lifecycle, with a significant emphasis on user provisioning.
Access Governance and Compliance (AGC) is another security framework for ensuring user accounts have appropriate and authorized access to organizational resources and data. AGC features are also foundational for IAM solutions, focusing on monitoring, reviewing, and validating user access for compliance with organizational and regulatory requirements.
AGC is sometimes referred to as a subset of IGA, and IGA and AGC are related to the Identity Governance Framework (IGF) specifications on the Oracle Technology Network. To avoid confusion, this article treats IGA and AGC as separate frameworks that are implemented for IAM user lifecycle management, access control, and account regulatory compliance.
Differences between IGA and AGC
The biggest difference between the two governance frameworks is what they focus on for IAM systems.
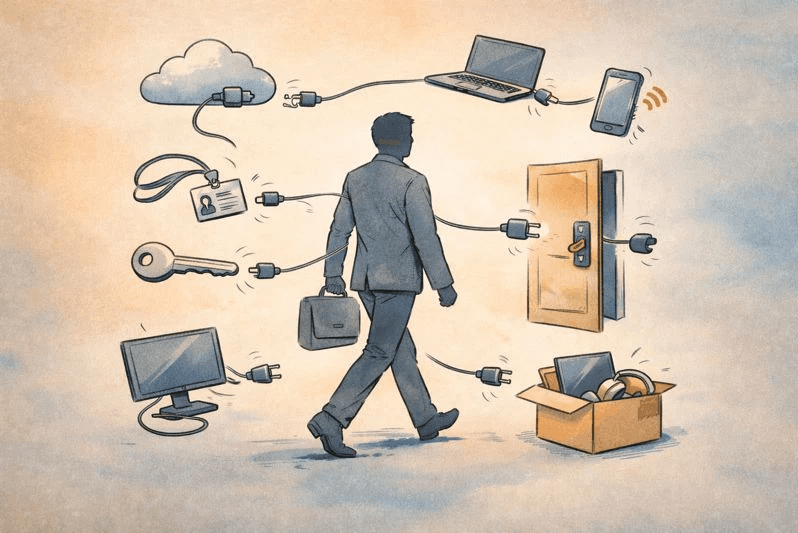
IGA focuses on automating and administrating the policies, procedures, and controls for provisioning IT system and data access. It serves as a comprehensive end-to-end framework for automating user lifecycle management across multiple systems. IGA features administer the joiner, mover, leaver process for user provisioning (onboarding, changing, and offboarding). They implement the principle of least privilege (PoLP) requiring that users only have the necessary (least amount of) permissions needed to perform their jobs.
AGC focuses on user account oversight and visibility. It automates the policies, procedures, and controls for ensuring user adherence (compliance) to relevant business, legal, regulatory, and other standards and requirements. For IAM user provisioning solutions, compliance encompasses audit trails, user account logging, documentation, access monitoring alerts, resolving access drift, audit reporting, and more. AGC features evaluate whether user access rights align with existing security policies and regulatory requirements.
IAM User Provisioning Capabilities for Identity Governance & Access Governance
To achieve IGA and AGC goals in your organization, look for Identity Management and Access solutions that provide the following capabilities.
IAM User Provisioning Capabilities for Identity Governance
Use IAM user provisioning solutions such as Tello that offer the following capabilities to meet IGA specifications.
Automated user provisioning and deprovisioning: Joiner, mover, leaver provisioning based on new hires, terminations, and role changes.
Automatic detection and importation of existing users and privileges between systems: Provisioning new users based on access rights and privileges provisioned on another system.
Automated provisioning, synchronization and attribute mapping with HR and Identity Source providers: User provisioning and deprovisioning activities based on changes in HR/Identity Source providers such as Workday or Active Directory (AD).
Connectors for SaaS apps: IAM plugins for user provisioning management across major SaaS applications such as Microsoft Entra ID, Google Workspace, Amazon Web Services (AWS), etc.
Directory synchronization for user account provisioning: Harmonizing user accounts with centralized identity repositories including AWS Directory Service, Google Workspace Directory, Microsoft Active Directory (AD), and Okta Universal Directory.
Role-Based Access Control (RBAC) with pre-defined roles: Provides consistent access authorization to groups of users rather than to individual users.
Support for cross-system identity management: Integration with identity management protocols, including System for Cross-domain Identity Management (SCIM), Security Assertion Markup Language (SAML), and REST APIs.
Related reading: Using Role-Based Access Control With Predefined Roles
IAM User Provisioning Capabilities for Access Governance & Compliance
Use IAM user provisioning solutions such as Tello that offer the following capabilities to meet AGC specifications.
Access drift detection and resolution: Detect and resolve when user access permissions unexplainably increase or drift away from authorized and approved assignments.
Access monitoring for policy violations or abnormal access activity: Continual monitoring for security policy violations and access anomaly detection.
Access policy and management: Defines and enforces policies governing how access is granted.
Access review and certification: Regular user access reviews to confirm current user access remains appropriate.
Audit trail and activity logging: Detailed logs of provisioning and access changes, user change request approvals, and other documentation for audit and compliance.
Compliance reporting: Audit and compliance reporting for relevant regulatory requirements.
Segregation of duties management: Detect and prevent users having conflicting permissions that can enable fraud or abuse (i.e., ability to create vendor accounts and authorize payments).
Related reading: Risk Prevention and Remediation for Identity Access Drift
Manual versus Automated IAM User Provisioning
User provisioning occurs on multiple platforms. Most users require at least 10–15+ accounts that are provisioned on different systems using different tools. Without an IAM solution, IGA and AGC activities are frequently performed using manual processing following instructions kept in a Word document or a spreadsheet. Manual processing complicates achieving IGA/AGC’s primary goals: ensuring all user accounts have appropriate and authorized access to organizational resources and data.
IGA and AGC goals are better served by using centralized IAM user provisioning tools such as Tello. Centralized tools automate and monitor the user provisioning process across multiple systems and services. They can also provide access review capabilities, audit logging, user provisioning reporting, alerts for policy violations and abnormal access activity, and the ability to flag and resolve identity access drift issues. Using centralized IAM user provisioning tools instead of relying on manual user provisioning is considered a best practice.
Learn more about user account provisioning
Contact us for more information on using innovative tools like Tello to modernize your user provisioning practices to IGA and AGC standards. Seasoft’s experts can perform an organization-specific assessment to help modernize your IAM user account provisioning and identity governance compliance.